How delivering outcomes changes everything in enterprise software deployment
Today’s business landscape is fast-paced and competitive. Software deployment enables businesses to adopt innovative solutions that boost security and operational efficiency.
However, adopting new enterprise software to streamline your business can be complex and time-consuming, requiring careful planning, expertise, and resources. This is where professional services offered by certified product experts come into play. Professional services provide you assistance and support throughout your entire deployment journey, ensuring a smooth and successful transition to go live and receiving full value from your software.
This article defines software deployment services, examines their importance, and shares elements of a successful initiative, like efficiency, risk mitigation, and maximizing your technology initiatives’ return on investment (ROI).
What is an outcome-based deployment model?
Previously, businesses rarely considered how customers used their products once delivered. In the traditional model, services were not considered a core offering alongside products. A new approach focuses on providing outcomes businesses achieve by combining products and services. This is known as outcome-based services, where companies have blurred the boundaries between products and services to deliver results.
What is enterprise software?
Enterprise software is the name used to refer to computer applications or systems specifically designed to meet the needs of large organizations. This type of software is typically developed to address complex business processes and workflows, and it provides a wide range of functionalities and tools to support various aspects of enterprise operations.
Enterprise software often encompasses multiple modules or components that integrate and interact with each other to facilitate seamless information flow across different departments or functions within an organization. It is intended to improve efficiency, productivity, and collaboration and enable better decision-making and strategic planning.
Some common examples of enterprise software include:
- Enterprise Resource Planning (ERP) systems
- Customer Relationship Management (CRM) systems
- Supply Chain Management (SCM) systems
- Human Resource Management (HRM) systems
- Governance, Risk, and Compliance (GRC) systems
Enterprise software is often highly configurable and extensible to meet your organizational requirements and can be deployed on-premises or accessed through cloud-based services. It plays a crucial role in modern businesses by enabling efficient and effective management of complex operations at scale.
What are outcome-based deployments?
In a digital world, you need deployment strategies that ensure you realize business outcomes with your enterprise software deployment. This is a shift from traditional deployment services focusing on the transactional or output-based process of deploying enterprise software and services.
SafePaaS’ SafeMethod™ focuses on developing deeper relationships and providing true business outcomes. Outcome-based deployments tie your project to measurable results, meaning you can directly measure their impact on your business. The greatest value of outcome-based deployments is their focus on delivering economic value.
Why enterprise software requires deployment by certified professional services experts
Enterprise software requires deployment by certified professional service experts for several reasons, including:
Streamline business processes: By leveraging deployment services, your organization can benefit from the experience, knowledge, and specialized skills of professionals to streamline and optimize your business processes. These services encompass process assessment, change management, performance measurement, training, best practice deployment, and ongoing support. Through these collaborative efforts, you can achieve streamlined processes that drive productivity, reduce costs, and enhance overall business performance.
Deliver outcomes: Deployment services contribute to your success by providing specialized expertise, an objective perspective, resource augmentation, time and cost savings, risk mitigation, training, and knowledge transfer. Leveraging deployment services allows you to tap into external resources and capabilities to achieve your desired outcomes more effectively and efficiently.
Manage integration: In many cases, enterprise software must integrate with your existing systems and applications. Deployment services are required to establish seamless data flow and communication between your new software and existing systems, ensuring that information is shared accurately and efficiently.
Right-size extensibility: Enterprise software is often designed to be highly extensible and to meet your specific needs. Deployment services help you tailor the software to match your unique business processes, data structures, and workflows. This extensibility ensures that the software aligns with your organization’s requirements and maximizes its value.
Secure deployment: Services are crucial for successfully deploying enterprise software, tailoring it to your needs, integrating it with existing systems, migrating data, training users, optimizing performance, and providing ongoing support. These services ensure the software is effectively deployed, adopted, and utilized to drive business efficiency and achieve your desired outcomes.
Data migration: Organizations often need to transfer data from legacy systems or manual processes when deploying new enterprise software. Data migration services help you extract, transform, and load your data into the new system while ensuring data integrity, consistency, and security.
Performance optimization: Enterprise software deployments involve configuring the system to achieve optimal performance and scalability. Deployment services help you fine-tune the software’s settings, infrastructure requirements, and performance parameters to ensure it performs optimally under your specific workload and usage patterns.
Training and change management: Enterprise software typically introduces significant changes in your business processes and workflows. Deployment services include training programs to familiarize your users with the new software and provide them with the necessary skills to use it effectively. Change management services help you transition to the latest software, address resistance to change, and ensure a smooth adoption process.
Ongoing support and maintenance: Deployment services include post-implementation support to address issues, provide software updates and patches, and offer ongoing technical assistance. This support helps resolve challenges and ensures the software remains updated and functional.
Benefits of enterprise software deployment services
Software deployment services refer to deploying and integrating software into your business workflow as part of your digital transformation strategy. Implementing new software is a resource and cost-intensive project. While accessing software can easily be achieved with cloud technology, you will have trouble moving forward if your software deployment does not go as planned or fails to deliver your desired outcomes.
A deployment plan is required if you want the process to go as smoothly as possible. Deployment services involve planning, configuration, customization, testing, training, and support to ensure your software solution’s successful adoption and utilization. Other benefits of software deployment services include the following:
Expertise and experience: Deploying software requires specialized knowledge and experience. By engaging software deployment services, you gain access to certified in-house professionals and partners skilled in deploying and configuring software systems effectively. They can leverage their expertise to streamline your deployment and avoid common pitfalls.
Efficient deployment: Software deployment services help ensure a smooth and efficient solution deployment. The service providers follow established methodologies and best practices to guide your deployment process, reducing the risk of errors, delays, and disruptions to your business operations.
Extensions and integration: Many enterprise software customers require extensions and integration with existing systems to meet specific business needs. Deployment services can help tailor the software to match your organization’s unique requirements. They can integrate the software with other applications, databases, or third-party services, ensuring seamless data flow and functionality.
Reduced deployment time: With dedicated resources and a structured approach, software deployment services can accelerate your timeline. Service providers have the tools, templates, and pre-built configurations to speed up the deployment process, allowing your business to benefit from the software solution sooner.
User training and support: A successful software deployment involves training your staff to use the new system effectively and to its fullest potential. Deployment services provide user training programs that familiarize your team with the software’s features and functionalities. They also offer ongoing support, helping users troubleshoot issues and maximize the software’s potential.
Risk mitigation: Software implementation projects carry inherent risks, such as data loss, security vulnerabilities, or disruption of operations. Professional deployment services employ risk mitigation strategies to minimize these risks. They ensure your data integrity, implement robust security measures, and perform thorough testing to identify and resolve issues and disruptions before the software goes live.
Long-term value: Software deployment services focus on the initial deployment and the long-term value and return on investment (ROI) for your business. They provide insights and recommendations on optimizing the software’s usage, improving business processes, and adapting to evolving needs. This ongoing support helps maximize the value you derive from the software solution.
Deployment services can save you time, reduce risks, improve efficiency, and enhance the adoption of your solution. Deployment services enable you to leverage technology effectively and realize the intended outcomes of your technology investment.
SafePaaS’ approach to the deployment services process
SafeMethod™
SafeMethod
The objective of enterprise software deployment services is the assurance of good outcomes. When purchasing transformational technology, you count on outcomes, not features, to deliver the desired result. With deployment services, you can trust that the outcomes will reduce expenses on your bottom line because you can increase productivity and efficiency while reducing errors, waste, and fraud and mitigating cyber threats.
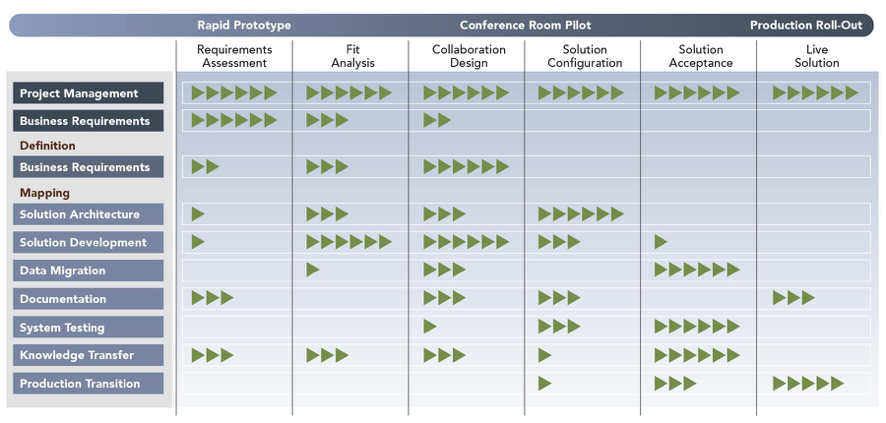
SafePaaS’ deployment approach has been developed and tested in hundreds of organizations. Our deployment methodology SafeMethod™ uses an iterative approach based on a hybrid of waterfall and agile methodologies. SafeMethod™ has various phases to rapidly deploy the solution to meet your outcome objectives.
Phase one: Business Requirement Definitions
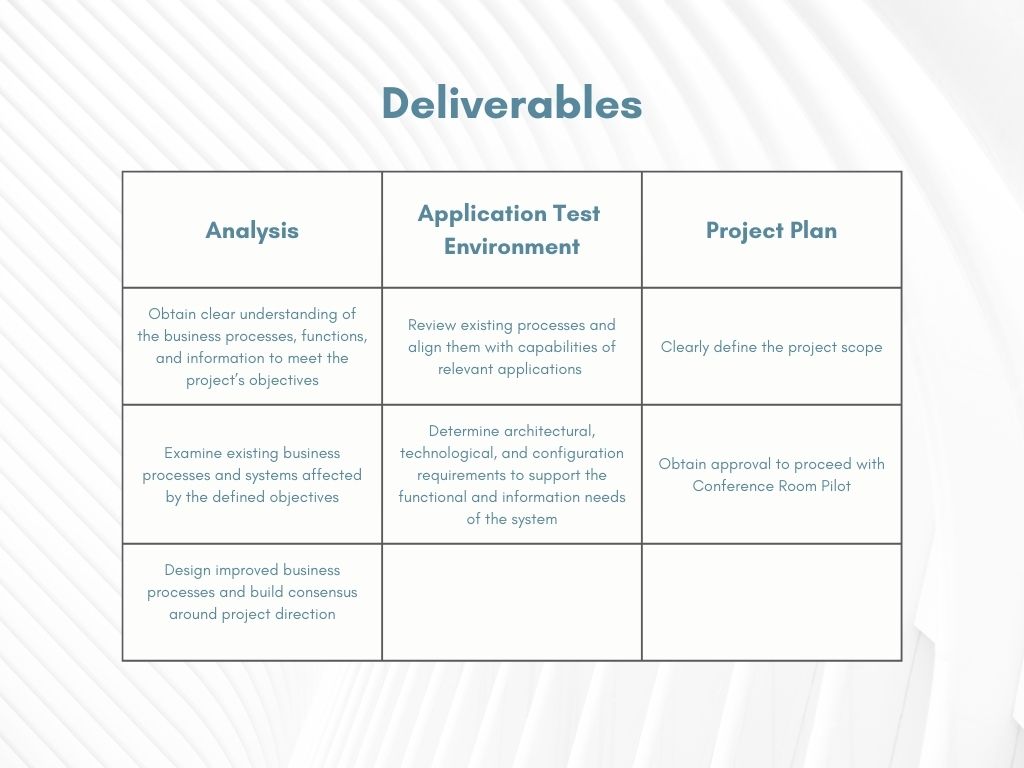
SafePaaS certified in-house and partner services teams works with you during the requirements phase to understand your needs in detail. We analyze your current processes and how things are done and determine your bottlenecks by looking at who does what and who is responsible for every step of your process.
SafePaaS also evaluates your current process and technology and the results that you’re producing. We provide a full 360-degree review and analysis of your requirements aided by the deliverables documentation used in the process tools, people, knowledge, and training. We provide a comprehensive understanding of your requirements against best practices developed over the years to ensure that we fully understand your needs in detail before we try to solve the problem with a solution.
The requirements definitions phase begins using structured, facilitated workshops. Each workshop includes a subject matter expert (SME) and a scribe to document your requirements. These requirement definitions are presented as deliverables at the end of the requirements phase to your stakeholders for review and approval. Understanding your requirements and process takes about two weeks and involves workshops on key topics. Area workshops can be between an hour to 90 minutes each.
Phase two: Analysis
The fit-gap analysis phase of SafeMethod™ is where you see your requirements, how many can be met, and how they can be met by mapping to your current solution. A skilled deployment service provider can look at your environment, compare your requirements against your capabilities and perform a fit-gap analysis. For example, if your organization is testing a control manually, our solution offers a way to automate your control testing instead of gathering data and samples. Or, if you reconcile purchase orders with three-way matches, you may want to look at a control within your ERP system or business application to enforce the three-way match. In other cases, there may be a unique situation where the proposed solution does not fit how you perform certain tasks. In those cases, we offer various software configurations to meet the requirement. We can find a solution and enforce an automated control 90% of the time. However, there is a small possibility a use case is not feasible upon implementation. In these cases, we offer a flexible approach where the enhancement requests by our engineering and product solutions team can be provided in a future capability. The fit-gap analysis phase can take one to two weeks.
Phase three: Solution design
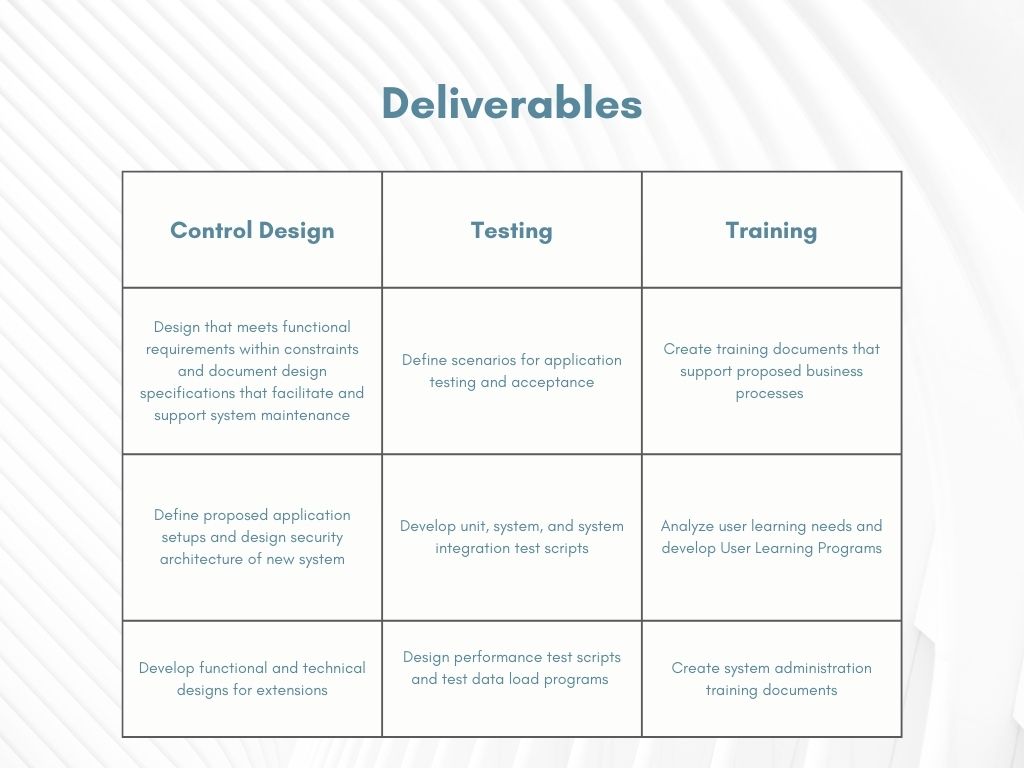
The third phase of SafeMethod™ is designing your solution. Our workshops are organized to configure the solution to demonstrate your requirements. We perform rapid prototyping and complete a collaborative design using your data, workflows, and other requirements allowing you to see your flows inside the software.
For example, if you need access certification, you can see the user’s identities and the workflow sent to the reviewers for access certification approval. This phase of the process is very helpful and has many benefits, including confidence that your requirements are understood and how the software can help. The design phase also helps SafePaaS clarify any requirements that may be unclear from the previous two phases, and new gaps can be identified during the collaborative design.
Some workshops involve participants from your audit, compliance, finance, and IT security teams and any others that will interact with the software. These workshops focus on key topic areas, like the requirements phase, and they run 90 minutes on average.
For example, a Segregation of Duties (SoD) workshop will include setting up and entering the SoD policies inside the system. The second workshop may be around processing those policies and generating the violations created by entering the policies.
The third workshop walks you through the outputs and workflows. Topics typically covered in the design phase are workflows, security roles, and role design. These topics cover how users input, process, and extract data from the system. The deliverable is revised and finalized for sign-off of the solution design that will proceed into your system.
Phase four: Configuration
The next phase in SafeMethod™ is the configuration phase, which requires limited participation on your end. Our configuration experts at SafePaaS can provide requirement design deliverables and configure the system because we are specialists in creating SoD policies, configuration controls, or connections to your enterprise application. Your systems are also documented with screenshots demonstrating deployment to the system. The solution configuration step is essential in making you self-sufficient in managing and deploying the SafePaaS application. You are also provided a configuration document with step-by-step instructions on how SafePaaS will be configured to meet your agreed-upon requirements in the design phase.
QA testing is performed when the QA team creates use cases or test scripts. For example, in SoD, we test the policies designed with various testing ranges. If an activity needs to be updated, a new privilege is introduced that requires the activity to be updated, or the role of the policy owner has to be changed.
SafePaaS has a library of use cases collected through field experience to accelerate the configuration process, and we have various tools to ensure each phase proceeds efficiently. In addition to having certified experts implementing our products, you will provide your own testing and gather evidence of the testing and results.
These results are then confirmed independently and verified to ensure the solution is configured to your requirements (known as traceability analysis), which means once the system is configured, we’ll trace the requirements to ensure that they are designed and configured in the system as agreed upon. It’s a possibility that some of the requirements may not be fully configured or have limitations, which will carry over into the next phase of the deployment, solution acceptance.
Phase five: Solution Acceptance
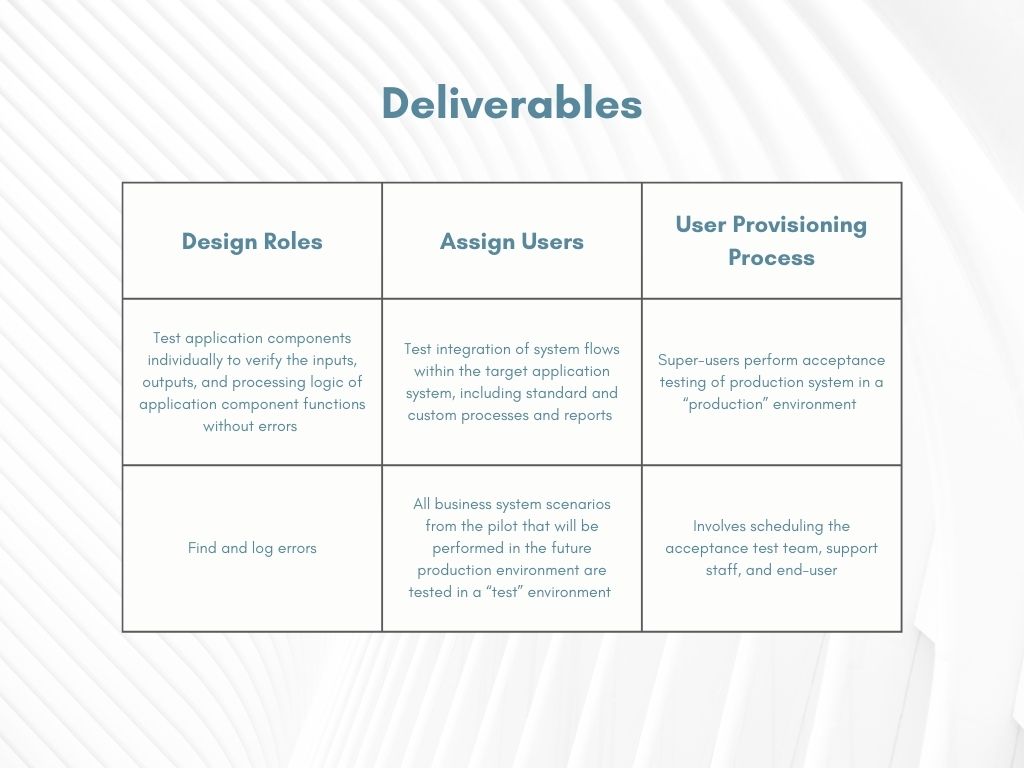
Before the system goes live, the first step is to train and provide you access to the system. SafePaaS uses many methods for training, including hands-on training, workshops, reviewing user guides, and even building special training, depending on the scope of your needs to roll the solution out successfully.
Independent testing is an integral part of solution acceptance. Testing allows you to review the results produced by SafePaaS during the configuration stage, and you can independently enter data into the system. This will enable you to look at the outputs and the results and collaborate on the solution.
For example, you can test the solution design in the sandbox instance. A typical environment strategy for deploying an enterprise system uses three application instances. The first instance is the sandbox, where we build, configure, and design your solution.
The second instance is user acceptance testing (UAT), where SafePaaS has read-only access, and you have full access. This gives you the independence to go in and test what you’ve learned in the sandbox by performing live exercises.
At this stage, any reported issues are logged in our issue-tracking system. We take responsibility for resolving them promptly and completely to your satisfaction, allowing you to build confidence and accept the system.
Next, we create a production migration document that you can use to deploy the solution into production. This is the production rollout, the last step before the solution goes live. During this phase, you provide documentation, data, and migration verification. For example, if you’re bringing in a security model from your ERP or business application like your ITSM, IGA, and IDM systems. All your data is mapped and verified clearly.
Lastly, the deployment stage pushes your solution into the production environment. Once the system is up, SafePaaS creates a production rollout checklist. These checklists are created to ensure configuration and migration are documented, performed, and applied and that all steps are completed as expected in the checklist. And that’s how SafePaaS deploys the system to meet your requirements.
SafePaaS deployment team roles and responsibilities
You need the right team and skill sets on your deployment team to successfully deploy and maintain your SafePaaS enterprise governance platform and realize maximum value and desired outcomes. Our certified in-house and partner teams will be dedicated to establishing, maintaining, and extending SafePaaS as a strategic business platform in your organization. Here are the key roles involved.
Project Manager
The Project Manager is responsible for the overall project delivery, including:
- Business requirements analysis
- Solution design and implementation
- Prioritizing service requests to SafePaaS
- Reviewing and approving
- Implementing processes and procedures within the time frame and agreed to by Client Project Manager
Risk Advisor
The Risk Advisor assesses ERP risks to select access, configuration, transaction, and embedded preventive controls for deployment to ensure that the investment results are risk mitigation based on the client’s risk tolerance by BU, Process, and ERP deployment.
Functional Lead
The Functional Lead conducts the analysis and design sessions according to the project timeline, including:
- In collaboration with the designated Client Lead Analyst, identify all business requirements that need to be mapped into the applications
- Transfer knowledge and skills of applications to the Client Lead Analyst
Training Manager
The training Manager provides on-site and online training to train the client project team according to the project plan, including:
- Deliver overview training, as well as step-by-step, hands-on training Prepare and deliver training material based on training objectives in scope
- Prepare a training environment to ensure the project team can log in and follow instructor-led exercises for effective knowledge transfer
Solution Architect
The Solution Architect guides the client IT team on the application compatibility matrix, server sizing, network bandwidth, and client IT standards based on expected application usage, including:
- Provides technical expertise to tune application configurations for optimal performance
Infrastructure Manager
The Infrastructure Manager provides installation and technical support during the project to maintain applications and resolve open issues, along with other team members, including:
- Assists in the testing and deployment of the application to facilitate timely deployment of the application to the production environment
Control Developer
The Control Developer develops, extends, tests, documents, and debugs business objects, control monitors, control elements, and ETL adaptors, including:
- Reviews requirements and design documents with the project team
- Perform unit testing and provide sample data for user testing
Analytics and BI Manager
Develop, extend, test, document, and debug data analytics schema and objects, including:
- Reviews reporting requirements with the project team
- Provides sample reports and unit test reports
ERP Controls Developer
The ERP Controls Developer designs, extends, tests, documents, and debugs ERP forms, workflows, and objects to prevent control failure and remove process bottlenecks, including:
- Reviews the requirements and design documents with the project team
- Performs unit testing and provides sample data for user testing
Client Project Manager
The Client Project Manager serves as a focal point for gathering, analyzing, and collating data and business information, including:
- To allocate, administer, and generally manage Client project resources, to provide strategic and short-term project planning support
- To provide support to team members and the SafePaaS Project Manager when required
Client Functional Lead
The Client Functional Lead brings specialized business knowledge to the project and performs the analysis of the workflow and requirements, writes business process flows and test scenarios, and provides testing and feedback, including:
- To assume direct responsibility for facilitating control modeling and workflow knowledge transfer to the project team
- To identify the resources in their area who have business process knowledge
- To assist in initial end-user training and provide all future end-user training
Client Technical Lead
The Client Technical Lead understands and maintains the Oracle applications environment and the various software application services connected to the Oracle applications environment, including:
- Maintain environment backups and recoveries, patch logs, follow up on technical TARs, maintain all instances at similar patch levels
- System and database administration
- Available to the project team for problem-solving
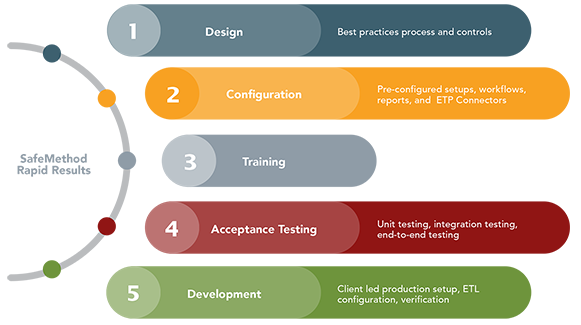
RapidResults™ – Agile accelerated deployment approach
RapidResults offers your organization an Agile accelerated deployment approach designed to address audit findings, meet compliance deadlines, or establish effective control governance processes. By leveraging pre-configured SafePaaS applications, controls, and workflows, RapidResults™ enables your organization to swiftly mitigate identified risks and adopt best practices.
To cater to immediate requirements, RapidResults provides access to pre-configured SafePaaS applications based on the comprehensive SafePaaS Controls Catalog. This ensures your organization can quickly implement the necessary controls without significant customization efforts.
Deployed with Agile methodology, RapidResults consists of iterative phases called “sprints.” Each sprint consists of backlogs based on epics and stories. Each story is carefully structured with defined tasks, acceptance criteria, responsibilities, and timelines within our automated project management tool. This approach accelerates the facilitation, progress tracking, validation of business requirements, and quality assurance for achieving rapid return on investment. After each sprint, a quality check is conducted to assess deliverables and ensure critical success factors are met.
Rapid results
Navigating today’s fast-paced and competitive business landscape requires businesses to harness the power of enterprise software. While deploying enterprise software can present challenges, certified deployment services experts offer an instrumental tool in overcoming these obstacles.
Deployment services play a vital role in ensuring a seamless and efficient implementation journey. With their expertise and support, you can successfully transition to the go-live stage and fully unlock the value of your software investment.
By understanding the impact of enterprise software and the significance of deployment services, you can make informed decisions and reap the rewards of enhanced security and operational efficiency. Embracing these solutions will empower you to stay competitive, adapt to ever-changing market demands, and propel your growth in today’s dynamic business environment.







