Access Analytics is a key component of an enterprise access governance solution as it can improve the effectiveness of controls and provide real-time insight to mitigate emerging threats. SafePaaS customers use access analytics in many ways and rely on results to safeguard their business against cyber security risks and insider threats from access policy violations.
Organizations require proactive and periodic analysis of growing threats to business applications and IT systems to support hybrid, agile and hyper-automation business needs. The traditional business intelligence and reporting tools are unable to cross-link changes to complex security meta-data against the fragmented, de-centralized provisioning process. Effective analysis requires not only the privileges assigned to employees, but also third parties, service accounts and BOTs to ensure compliance with access governance policies.
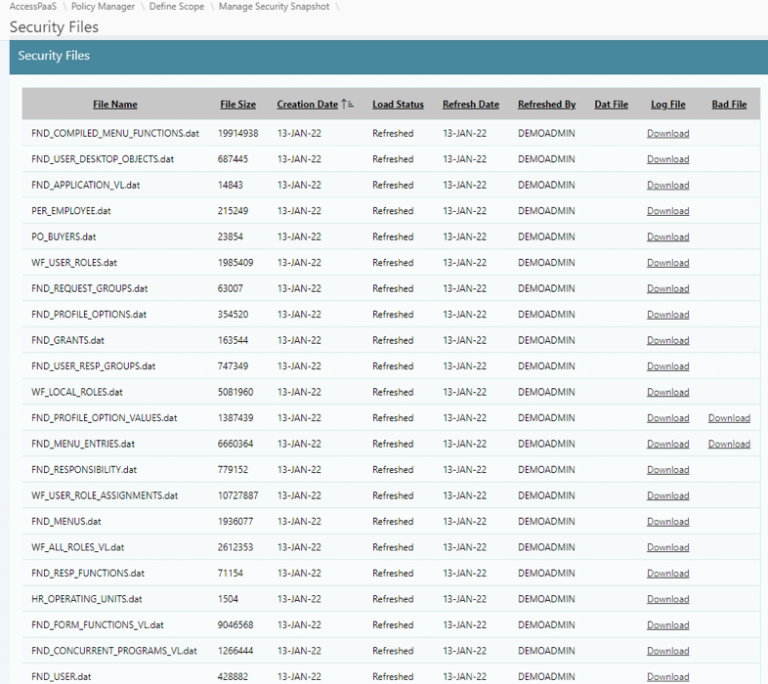
SafePaaS Advanced Analytics enables you to “find the needle in haystack” by using discrete as well as fuzzy logic to filter historical data sets stored in SafePaaS, and perform What-if analysis to predict potential risks that would impact business applications and IT systems. Advanced data comparison options ensure that requested corrective actions to security are completed timely. Changes introduced by third-party application providers are detected and alerts are routed to IT security personnel for examination and remediation. Auditors can ensure that access controls are operating effectively by analyzing ITSM request logs against the fulfilment records in business and IT systems. Application administrators can ensure that the user access to applications is terminated when employee jobs assignment are changed or terminated in HR systems to prevent orphaned or dormant access.
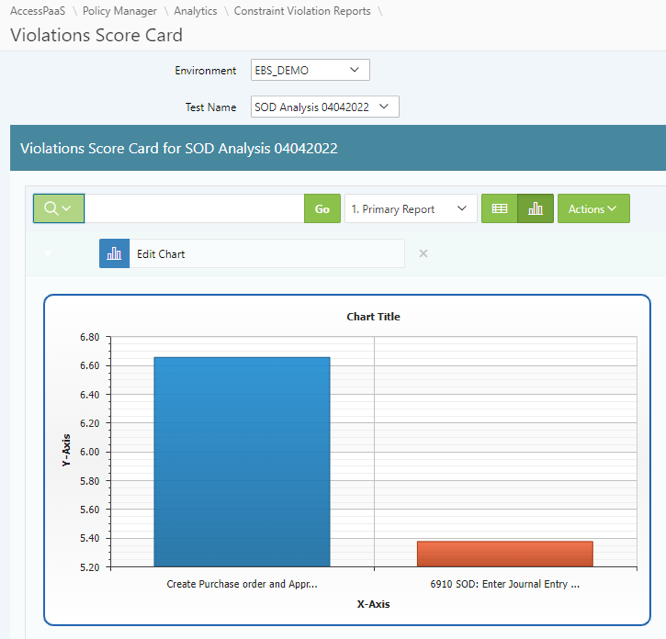
Provides a summary of access risks by policy, business unit, and application. The report can be viewed in tabular form or graphed using standard functionality available throughout the platform. Frequently used by executive management to assess the overall access risks and monitor progress against the remediation plans.
Provides inherent risk in the business role configurations, including the component and attribute details that grant privileges to the role. Frequently used by application administration to redesign and reconfigure out-of-the-box roles provided by application vendors that don’t comply with access policies.
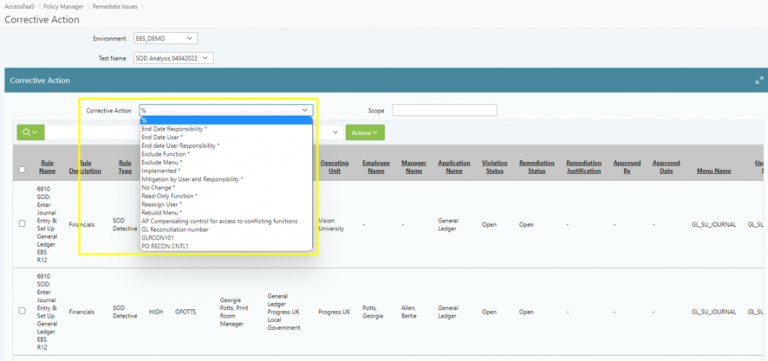
Provides detailed status of corrective actions workflows by action type such as request to change assignments, reconfigure roles, or modify access control attributes within the security model such as data groups, profiles, business units, and authorization limits. Control Owners and IS security teams use these reports to ensure the remediation plan is completed on time and results are verified.
Provides inherent risk in the business role configurations, including the component and attribute details that grant privileges to the role. Frequently used by application administration to redesign and reconfigure out-of-the-box roles provided by application vendors that don’t comply with access policies.
Auditors require look-back analysis, to review prior-period evidence to evaluate the effectiveness of access controls management process by detecting incidents where the potential risk detected during the audit analysis may have materialized.
For example, Segregation of Duties (SoD) controls analysis identifies the users that can violate one or more SOD policies. Once the violations are detected, and the majority of the risk is remediated or mitigated by fixing security roles or changing user access assignments, the remaining unmitigated “residual” risk requires lookback analysis. Residual risks exist in the majority of the complex ERP systems because the remediation process is labor intensive and costly or it requires the organization to make changes to the process or increase in personnel – which is time consuming and over the budget. Residual risk requires auditors to perform lookback analysis to detect user that performed conflicting activities where the risk was not mitigated. For example, if users in the payable department had the ability to Create a Supplier and Pay a Supplier, how many of those users actually performed such transactions during the audit period. This analysis qualifies Segregation of Duties risks by identifying and quantifying the financial exposure from SoD violation transactions e.g., creating a supplier and paying that same supplier. This type of analysis, historically a monumental task, can be automated with SafePaaS Advanced Analytics.
Thank you for reaching out. If you have any questions, inquiries, or require assistance, please don’t hesitate to contact us using the form below. A member of our team will respond to your message as promptly as possible.
