Enterprise iAccess™ (EIA) enhancements
SafePaaS customers can prevent access risks in cloud, hybrid and on-premise identity life cycle management with Enterprise iAccess™ (EIA)
Digitalization and the constant evolution of business as well as IT landscapes together with the increased adoption of hybrid work models, along with legacy on-premise applications have materially increased the risks in Identity Lifecycle management.
Organizations with disparate IT systems, require Identity Life Cycle Management solutions to control access for onboarding employees, contractors, and third parties.
Any change to work assignments, or departures from the organization requires immediate updates to security privileges in compliance with access governance policies to ensure users only have access to what they need while removing access they don’t need. Policy-based access management also improves user productivity while preventing unauthorized users from accessing business-critical systems.
EIA enables SafePaaS customers to automate identity lifecycle management by adopting industry best practices
For example, EIA now enables customers to adopt the (ISC)² security framework to automate and control the identity lifecycle in the context of the following phases:
-
Provisioning
-
Deprovisioning
-
Access Review
-
Defining new roles
-
Account Maintenance
(ISC)², the International Information System Security Certification Consortium, is the world’s largest IT security organization that offers the most widely known security certification – Certified Information Systems Security Professional (CISSP)
Many customers are upgrading to Enterprise iAccess because legacy Identity life cycle solutions, adopted over the last two decades have left IT systems exposed to risk because onboarding and offboarding are performed at an abstract role level – without any policy based access controls.
EIA can be used on its own or as an extension of your existing Identity Management such as Microsoft Azure, Okta, Onelogin and other IDM softwares that support web services such as SAML, REST and SOAP.
EIA includes self-service access request management services to ensure that user access service requests are managed in a streamlined manner. Customers that have already deployed the iAccess self-service solution have reported significant reduction in IT help desk costs and errors. Customers interested in improving cybersecurity, productivity, agili,ty and responsiveness should consider EIA to improve the Lifecycle Management process.
EIA can create a new account for a new employee. The fulfilment process ensures that the approved access adheres to the “Principle of Least Privilege” for optimal security. Also, the critical risk in the deprovisioning process is mitigated by timely fulfilments of termination requests in IT systems to prevent risk of dormant and orphan accounts – which can be misused by insider and external bad actors to access sensitive data.
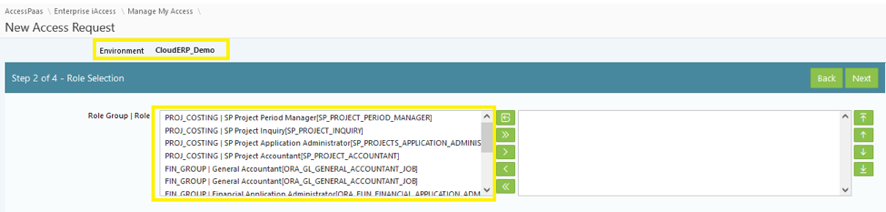
Self-Service enables requesters such as employees, contractors and third-parties to independently ask for roles with any of the business applications and IT infrastructure available in the roles catalog:
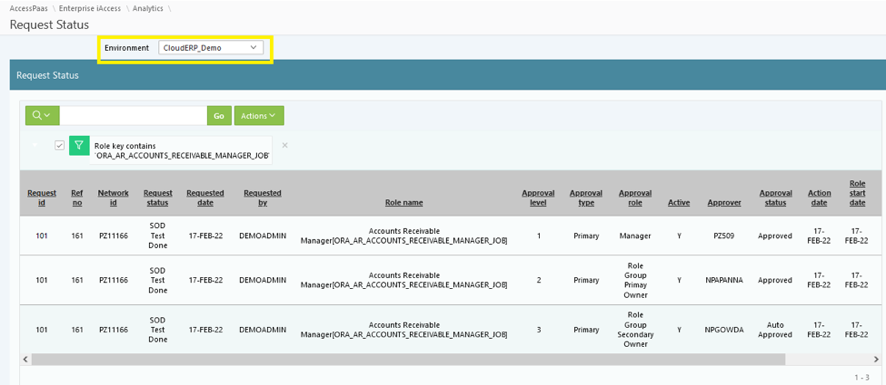
Requesters receive email notification as the request workflow move through the approval process – improving help desk service levels and overall IT service productivity. Requesters can all view the status of all request within SafePaaS:
Customers that are currently using iAccess for a single ERP system such as E-Business Suite, can migrate to Enterprise iAccess to improve access governance, based on compliance policies, to achieve enterprise wide Identity Orchestration.
Contact us for more information.







