A Message from our CTO, Hennie Vermeulen
As organizations continue to adopt AI and cloud applications, safeguarding data and managing enterprise risk has never been more critical. At SafePaaS, we are committed to delivering solutions that not only help you maintain control over your environment but also provide clear visibility into potential risks.
We are excited to introduce the following, designed with your needs in mind:
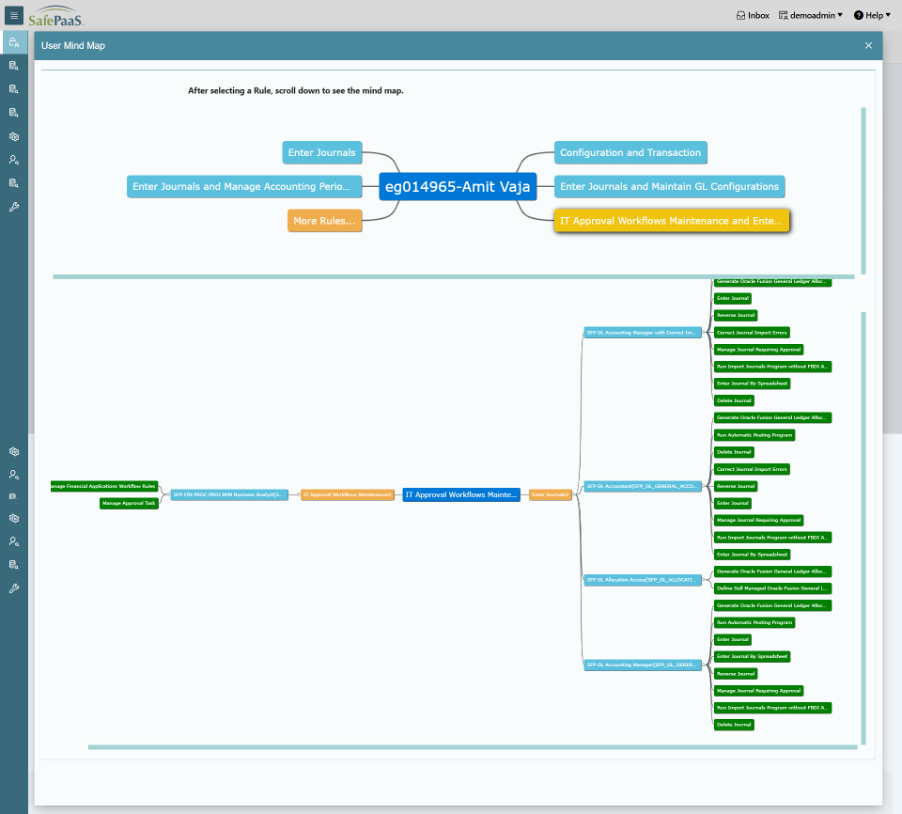
1. Precision Risk Mapping with Mind Maps
One of the challenges many of our customers face is identifying user access violations, such as segregation of duties conflicts. This challenge has grown as organizations adopt multiple SaaS applications, making it harder to pinpoint hidden risks. Our new mind map capability allows you to visualize and detect these risks with precision. By identifying vulnerabilities faster, your enterprise can reduce risk more quickly, ensuring compliance and strengthening your security posture.
2. Role Scoping for Identity Groups
Identity access reviews are a cornerstone of strong governance, but they can be time- consuming and costly. Our new risk-based approach prioritizes the identities that require frequent reviews while reducing effort on low-risk identities. This enables faster, more effective certifications while maintaining compliance and mitigating risk—a critical capability as organizations strive to align with standards such as NIST and ISO frameworks.
3. Enhanced Infrastructure and Data Control
We recognize that confidence in your data is paramount. Our updated infrastructure now allows self-service backups and recovery for Enterprise Access Monitor. This empowers your organization to retain full control over your data, supporting growing governance and security requirements as outlined in modern cybersecurity frameworks. These enhancements reflect our commitment to giving you the solutions to manage risk, maintain compliance, and drive operational efficiency—helping you stay ahead in an increasingly complex digital landscape.
At SafePaaS, our commitment is to Federated Governance — not just identity management. We believe that strong governance transforms access from a security checkbox into a strategic enabler for business resilience, agility, and trust.
Introducing Mindmaps
Segregation of Duties reports often result in data fatigue.
Organizations struggle with:
- Complexity Overload: Violation reports are traditionally too complex to understand easily, making it difficult for stakeholders to quickly grasp the severity of risks.
- Context Fragmentation: In a standard table, the relationship between a user and their assigned Roles, the specific Rule violated, and the underlying Privileges is often obscured across multiple rows and columns.
- Action Paralysis: Without a clear visual structure, users find it challenging to decide on the specific actions needed to remediate or mitigate identified risks.
Customer Value:
The primary objective of introducing a visual representation via a mindmap format is to simplify complexity.
Business Value:
- Immediate Insight: By providing a visual representation of complex risks upfront, the design ensures they are easily understood by both technical auditors and business process owners.
- Structured Clarity: Data is presented in a structured way that helps gain better insights into the violation output in a less complicated manner.
- Decision Support: The intuitive layout allows users to decide on remediation paths more effectively.
- Context Preservation: Mindmaps ensure that users never lose context of the “Who”, and “What” while investigating the “How”.
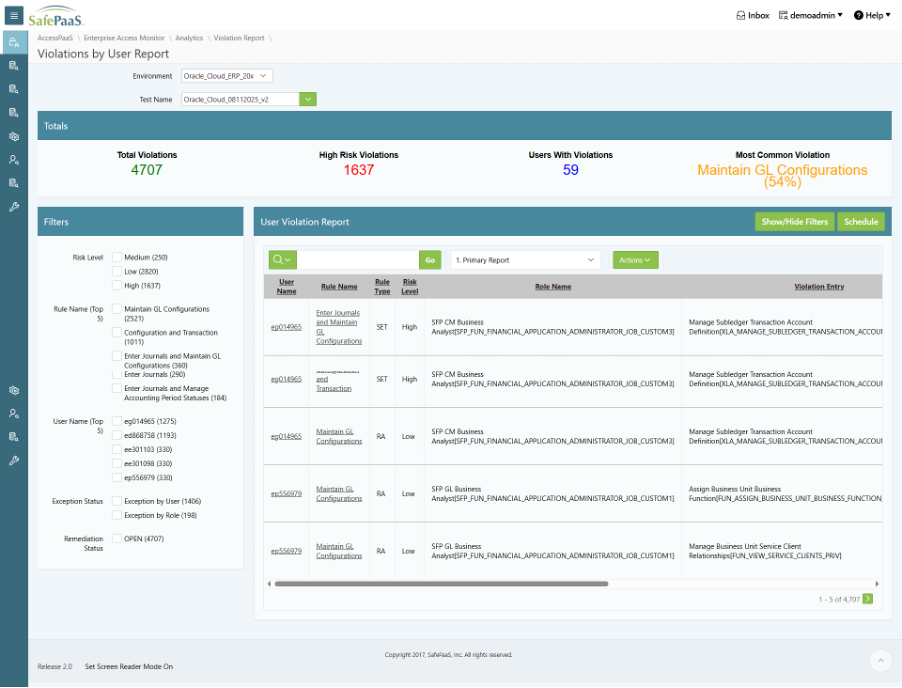
What and How it Works in SafePaaS
This solution enhances the existing Violations by User Report and the Violation Report in Roles
Manager.
What it is:
It is a hybrid reporting interface that combines a Summary Dashboard, a Faceted Search Filter
Panel, and an interactive Mindmap modal.
How it works:
- Summary Dashboard: Before the report begins, a new section displays high-level SoD
metrics, such as Total Violations, High-Risk Violations, Total Risk Exposure (in dollars), and
Overall Compliance Status.
- Faceted Filtering: Users can drill down into data using a filter panel (e.g., by Risk Level, Rule, or User).
- Entry Points: The system adds hyperlinks to the Rule Name and User Name columns.
o Clicking a Rule: Renders a mindmap showing all Users violating that specific rule
and the associated privilege paths.
o Clicking a User: Renders a mindmap showing all Rules violated by that specific user.
- Modal Rendering: To keep the user focused, the mind map opens in a Modal window. This
view automatically carries over any filters previously applied to the main report.
- Data Hierarchy: The mindmap visually connects the Rule/User to Activity Sets, Roles, and
specific Privileges (e.g., Privilege 1, 2, 3), allowing the auditor to trace the exact source of
the conflict.
Introducing Role Scoping for Identity Groups
Business Pain Point
The current Identity Group-based certification process lacks the flexibility required for role-specific scoping, resulting in a uniform approach that may not meet diverse attribute requirements:
- Overly Broad Review Scope: Currently, the system includes all roles assigned to a user for review. This forces reviewers to sign off on numerous roles, many of which are irrelevant to the specific certification campaign.
- Inefficient Reviewer Experience: Reviewers are burdened with excessive data, leading to an inefficient process where critical roles might be overlooked due to the sheer volume of low-risk roles.
- Attribute Maturity Issues: The current UAR automatically excludes attributes. For organizations that are not mature enough to review at this granular level, this creates significant unnecessary effort and work.
Customer Value
This enhancement shifts the focus from “quantity” to “quality” in the access review process:
- Targeted Risk Management: Administrators can now narrow the focus to only the most critical or relevant roles, maintaining a simple and effective review for the business.
- Audit-Ready Documentation: By requiring a justification for scoping decisions, the system creates a clear audit trail of why certain roles were prioritized over others.
- Operational Flexibility: Organizations can choose to exclude complex attribute-level reviews if they are not yet at that stage of GRC maturity, reducing the “noise” for the end-user.
- Consistency: The feature ensures that company-level configuration options are applied consistently across all identity-based access reviews.
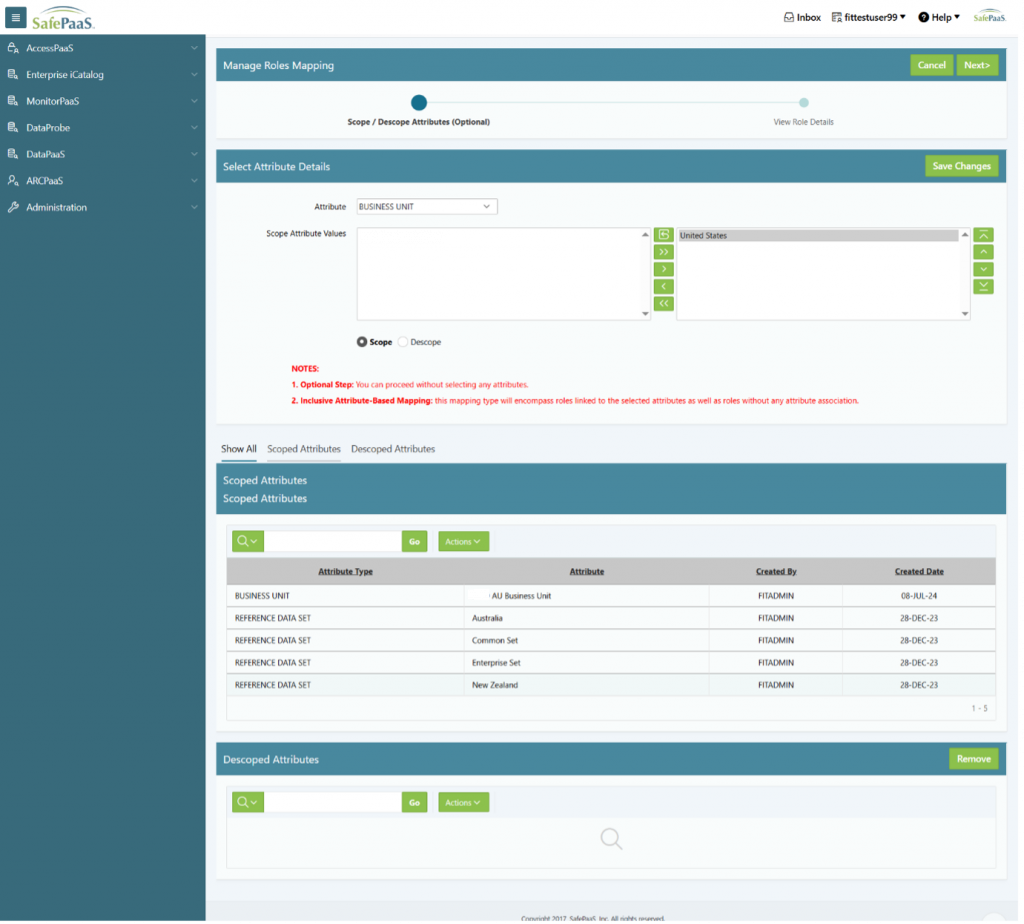
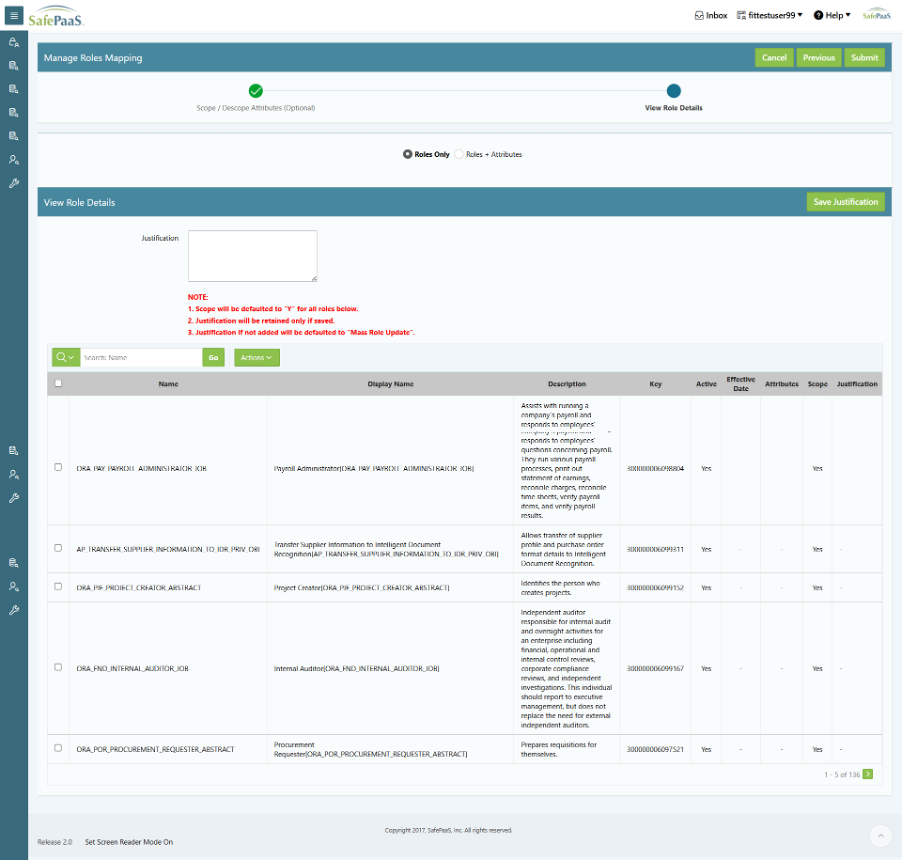
What and How it Works
This feature introduces a Role Scoping capability within the existing certification setup.
What it is:
It is a conditional configuration layer added to the Enterprise Access Certification Setup that allows for the selective inclusion of roles in an Identity Group review.
How it works:
- Conditional Visibility: A new tab titled “Scope Roles” appears only when the certification is configured at the Identity Group level.
- Role Selection (Interactive Report): Administrators are presented with a searchable report of all roles assigned to users.
- Scope Flag: Each role has a “Scope” dropdown (Yes/No).
- Mandatory Justification: If an administrator selects “Yes” to scope a role, they must provide a text-based Justification for why that role is included.
- Review Generation:
- When the review is triggered, the system only generates review items for roles marked “Yes”.
- Roles marked “No” are completely omitted from the reviewer’s view.
- Fallback Logic: This is an optional step. If an administrator does not scope any specific roles, the system defaults to the current behaviour and includes all roles and attributes for the review.
- Persistence: Once selections are saved and the certification is activated, the configuration is locked to ensure the integrity of the audit.
Enterprise Access Monitor Data Backup and Restore
A new utility that allows authorized users to back up an existing Enterprise Access Monitor environment and restore it to a new environment of the same application type. You can generate an encrypted zip file (containing CSVs) using PGP keys for secure transmission and restoration.
Business Drivers
- Policy Mandates
- NIST framework alignment
- Data Leak Prevention
Customer Value
- Essential component of cyber resilience and business continuity, ensuring that your data remains available and recoverable in the face of various threats.
- Protects your data by backing it up and restoring it separately, in line with rules that prevent data from being mixed.
- Adaptability and Flexibility: can be tailored to meet enterprise needs, rather than relying on a rigid, prepackaged approach.
- Implementation Efficiency: immediate benefit by speeding up implementations and acting as a configuration setup document
Data Included in the Backup:
- Security tables
- Snapshot details
- Violation data
- Exceptions
- Remediations
- SOD rules (all rules, whether approved, revised, or new)
- The latest SOD test violation results
- Data validated through analytics, such as user listing
Delivering More Value Through Gartner-Guided Strategy
We are thrilled to announce a strategic relationship with Gartner, one of the world’s leading technology research and advisory firms. This partnership will provide us with ongoing guidance on our product roadmap and strategic direction, informed by insights from Gartner’s thought leaders and deep market research. By leveraging their expertise, we can ensure that our solutions continue to align with emerging trends in cybersecurity, identity governance, and enterprise risk management—helping us deliver even greater value, innovation, and confidence to our customers.
Unlock Identity GRC Expertise: Join Michael Rasmussen, GRC 20/20 Founder, for Exclusive Events
We are honored to have Michael Rasmussen, the visionary who coined the term Governance, Risk, and Compliance (GRC) and founder of GRC 20/20, sharing his expertise with our customers. Michael’s decades of experience and deep insights into governance, risk management, and compliance will help our customers better understand emerging GRC challenges and how our solutions can address them. As part of this collaboration, we are thrilled to offer three exclusive, complimentary events throughout the year where Michael will provide independent, top-of-the-line insights, answer questions, and explore practical approaches to solving complex GRC issues. These events are designed to give our customers unparalleled opportunities to learn, engage, and stay ahead of trends in governance, risk, and compliance.
The first of these exclusive events is on March 18 in Chicago: Identity Governance and Risks in the age of multi-cloud and Agentic AI. Michael Rasmussen will share his expert insights on identity governance, risk management, and how organizations can stay ahead of emerging compliance challenges. This is a unique opportunity to hear directly from one of the most influential thought leaders in the GRC space and gain practical guidance on strengthening your enterprise controls.
Peter Hodge, Cyber Security Leader (Deloitte), author of White Blaze Leadership: Find your way to lead in the everyday, will also be in attendance and available to sign copies of his book.
Customer Impact Stories
How Industry Leaders Strengthen Governance with SafePaaS
Segregation of Duties for Microsoft Dynamics
A UK-based multinational food retailer recently strengthened its internal controls with SafePaaS.
By leveraging our platform to run a thorough Segregation of Duties analysis in Microsoft Dynamics, they were able to pinpoint potential conflicts, align user roles effectively, and reduce risk across their operations. The result? Greater compliance, stronger accountability, and a team empowered to focus on business growth instead of manual checks.
A leading South African food packaging company strengthens its access governance with compliant lifecycle management.
The company leverages SafePaaS iAccess to ensure users receive segregation-of-duties–conflict-free access in Oracle ERP. By validating access requests against SoD rules before provisioning, the customer eliminates risky role combinations at the source, improves compliance, and streamlines onboarding and access changes. The result is proactive risk prevention, stronger controls, and confidence that access is right the first time.
Fortune 500 Gaming Leader Strengthens Oracle Segregation of Duties Controls with SafePaaS
A Fortune 500 gaming company recently modernized its segregation of duties (SoD) risk management by migrating from a legacy GRC platform to SafePaaS. The legacy system had become difficult to maintain, with manual processes, slow audits, and limited visibility into Oracle roles and access risks.
By adopting SafePaaS, the company automated SoD analysis, simplified rule management, and gained real-time visibility across Oracle financial and operational roles. Compliance and IT teams can now conduct faster access reviews, generate clearer audit reports, and proactively remediate risks.
The migration has improved compliance efficiency, strengthened internal controls, and provided confidence in meeting complex regulatory and audit requirements.
Leading Semiconductor Company Streamlines Access Reviews with SafePaaS
A leading semiconductor company modernized its access review process by leveraging SafePaaS to gain greater visibility and control across its enterprise systems. Operating in a fast-paced, highly regulated environment, the company needed a scalable solution to manage user access efficiently while meeting audit and compliance requirements.
With SafePaaS, the organization automated access certifications, centralized reviewer workflows, and simplified remediation. Business and IT stakeholders now receive clear insights, enabling faster and more accurate access decisions without relying on fragmented tools.
As a result, the company significantly reduced the time and effort required to complete access reviews, improved audit readiness, and strengthened governance over critical systems. SafePaaS’s intuitive reporting and automation have allowed teams to shift from reactive compliance to a more proactive, risk-focused approach supporting both security and business agility as the company continues to grow.
Leading Thoughts and Industry News
Unlock Better Governance for Oracle ERP Cloud: Modern Risk and Identity Access Governance
Managing identity, access, and risk in Oracle ERP Cloud is complex. Weak controls can lead to audit failures and security gaps. This article explains why default roles and manual governance fall short, and how modern identity access governance practices help enforce least-privilege access, monitor sensitive activities, and keep compliance under control. It also highlights the need for continuous monitoring and tailored access policies so you can secure your cloud ERP environments and stay audit-ready.
From Static Roles to Dynamic Policies: The Next Era of Access Control
Traditional role-based access control is struggling to keep up with modern, dynamic enterprise systems where identities, privileges, and risks change constantly. The article explains why moving from static roles to policy-based access reviews lets organizations evaluate access in real time based on context, reducing exposure and audit pain. It also highlights how this shift moves governance from periodic checks to continuous assurance, helping you spot and respond to risks faster.
How CISOs Are Replacing Legacy IGA with Policy-based Access Governance — And Delivering Audit-Ready Assurance
CISOs are starting to rethink identity access Governance and are moving away from outdated tools toward modern, policy-based access governance to better manage risk and keep up with ever-changing compliance demands. The article explains how unified, real-time access governance helps reduce audit effort, improve risk visibility, and make audit preparation smoother and more reliable.
RELEASE SUMMARY – Enhancements and Features
02-Oct-2025 12:00AM
EIC-29
Administration
Enhanced object configuration by adding a button to automatically load metadata (objects and attributes) into Enterprise iCatalog.
02-Oct-2025 12:00AM
EIA-363
EIA>Manage My Access
Enhanced the Roles API to process the user access requests without error display
16-Oct-2025 12:00AM
SFP-1062
MTP>Dashboard
Introduced a new feature to display MonitorPaaS results in dashboards
13-Nov-2025 12:00AM
EAM-1544
EAM>Analytics>Violation Report
Enhanced violation reports for cross-application incidents
27-Nov-2025 12:00AM
EAM-1500
EAM>Detect Violations>Manage SOD Test
Enhanced validation of pre-requisite steps (e.g. snapshot failure) before submitting the SOD Test.