Managing Segregation of Duties risk doesn’t always mean removing access. Sometimes, the smarter path is monitoring the risk you’ve chosen to accept.
The Segregation of Duties Compliance Challenge Every Organization Faces
Segregation of Duties (SoD) is a foundational control in enterprise governance. The principle is simple: no single individual should have access that allows them to execute conflicting business functions without oversight. A user who can both create a vendor and approve payments, for example, creates a risk that organizations cannot afford to ignore.
Most GRC platforms effectively detect these violations. The harder question is what happens next. Remediation — removing the conflicting access — is the textbook answer. But in the real world, remediation isn’t always possible. Business-critical users may legitimately need conflicting access to do their jobs. Removing access could halt operations, delay financial close, or create bottlenecks that cost more than the risk itself.
This is where mitigation controls become essential. But before diving into mitigation, it helps to understand where SoD fits within the broader landscape of compliance frameworks and how a structured risk review process works end-to-end.
Segregation of Duties in the Context of Compliance Frameworks
Segregation of Duties is not an isolated compliance requirement. It sits at the intersection of several major governance frameworks that enterprises must satisfy:
SOX Section 404 (Sarbanes-Oxley Act) requires management to assess and report on the effectiveness of internal controls over financial reporting. SoD is one of the most visible control categories because conflicting access to financial systems creates direct risk of material misstatement. Section 302 further requires CEO and CFO certification that controls are operating effectively — meaning SoD violations without documented treatment are a direct certification risk.
COSO Internal Control Framework (2013) provides the conceptual backbone for how organizations design, implement, and evaluate internal controls. SoD maps to multiple COSO components: Risk Assessment (identifying where conflicting access creates exposure), Control Activities (implementing segregation and compensating controls), Monitoring Activities (ongoing validation that controls are working), and Information and Communication (reporting control status to stakeholders).
COBIT 2019 addresses SoD through several process areas. DSS05 (Manage Security Services) covers logical access controls and separation of duties. DSS06 (Manage Business Process Controls) addresses transaction authorization and segregation. APO12 (Manage Risk) governs the overall risk management lifecycle, and MEA02 (Monitor, Evaluate, and Assess Internal Controls) covers the ongoing assessment of whether controls are effective.
Industry-Specific Regulations layer additional requirements on top. HIPAA demands access controls to protect PHI. PCI DSS requires separation of duties for payment card environments. GDPR privacy requirements create access segregation needs around personal data processing.
The common thread across all these frameworks is clear: it is not enough to detect access conflicts. Organizations must demonstrate that every identified risk has a documented treatment — either eliminated through remediation or managed through compensating controls.
The End-to-End SoD Risk Review Process
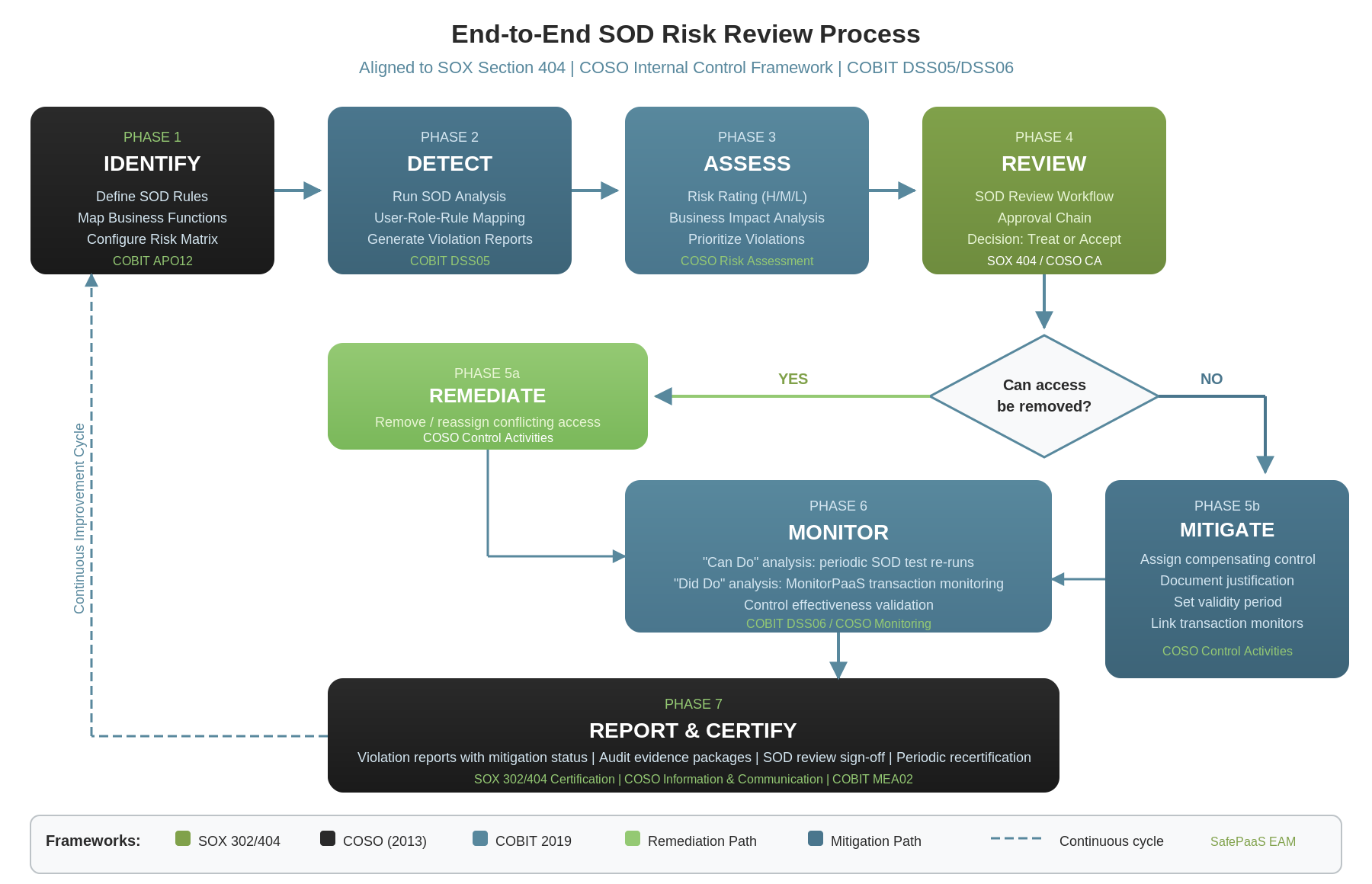
A mature SoD compliance program follows a structured seven-phase lifecycle that aligns directly with the frameworks described above:
Phase 1: Identify — Define Your SoD Ruleset
The process starts with defining what constitutes a conflict. Organizations map their business functions, identify which combinations of access create risk, and codify these as SoD rules in their GRC platform. In COBIT terms, this is APO12 — identifying and cataloging risk. The SoD rule matrix defines conflicting function pairs, assigns risk ratings (high, medium, low), and establishes the foundation for all subsequent analysis.
Phase 2: Detect — Run SoD Analysis
With rules defined, the platform analyzes user access against the rule matrix to identify violations. This is the “can do” analysis — identifying every user who holds access to both sides of a conflicting function pair. SafePaaS maps this at the user-role-rule level, producing detailed violation reports that show exactly which access grants create each conflict.
Phase 3: Assess — Evaluate and Prioritize Risk
Not all violations carry the same weight. A high-risk conflict in accounts payable demands more immediate attention than a low-risk conflict in a reporting module. This phase applies the COSO Risk Assessment component — evaluating the likelihood and impact of each violation to determine treatment priority. Organizations categorize violations by risk rating, business impact, and the sensitivity of the transactions involved.
Phase 4: Review — SoD Review Workflow
Violations are routed through an approval workflow where designated reviewers examine each conflict and decide on a treatment path. This is where SOX 404’s requirement for control effectiveness testing meets COSO’s Control Activities component. Reviewers assess whether the access can be modified (remediation) or must be accepted with oversight (mitigation). Every decision is documented with justification.
Phase 5: Treat — Remediate or Mitigate
This is the critical decision point. For violations where access can be removed without business disruption, remediation eliminates the risk entirely. For violations where the user legitimately needs conflicting access, mitigation controls provide the compensating oversight. Both paths require documentation, accountability, and audit trail.
Phase 6: Monitor — Ongoing Validation
Treatment is not a one-time event. Remediated violations need verification that access changes took effect. Mitigated violations need continuous monitoring — both periodic SoD re-testing (“can do” analysis) and transaction-level monitoring through MonitorPaaS (“did do” analysis). This maps to COSO’s Monitoring Activities and COBIT’s DSS06 process controls.
Phase 7: Report and Certify — Audit Evidence
The cycle completes with comprehensive reporting that demonstrates full risk treatment coverage. Reports show every violation alongside its treatment status — remediated, mitigated, or pending action. This provides the evidence base for SOX 302/404 certification, audit committee reporting, and external audit support.
The process is inherently cyclical. As access changes, new systems deploy, and business processes evolve, the cycle repeats — ensuring SoD compliance is maintained continuously rather than assessed only at point-in-time intervals.
What Are Mitigation Controls?
A mitigation control is a compensating measure applied to an SoD violation when the conflict cannot be resolved by removing access. Instead of eliminating the root cause, mitigation acknowledges the risk and puts structured oversight in place to manage it.
Think of it this way: remediation removes the ability to cause harm. Mitigation ensures that if something goes wrong, it gets detected and addressed promptly.
In practice, a mitigation control typically involves:
- Defining the control: A named, documented control with a clear description of what it monitors and why
- Setting a validity period: Start and end dates that ensure the control is time-bound and subject to periodic review
- Assigning to specific violations: Linking the control to particular user-rule-role violation patterns
- Associating with transaction monitors: Connecting the control to real-time monitoring that tracks whether the user actually performed conflicting transactions (the “did do” versus the “can do”)
- Requiring justification: Documenting why remediation isn’t feasible and why mitigation is acceptable
Remediation vs. Mitigation: Two Sides of Risk Treatment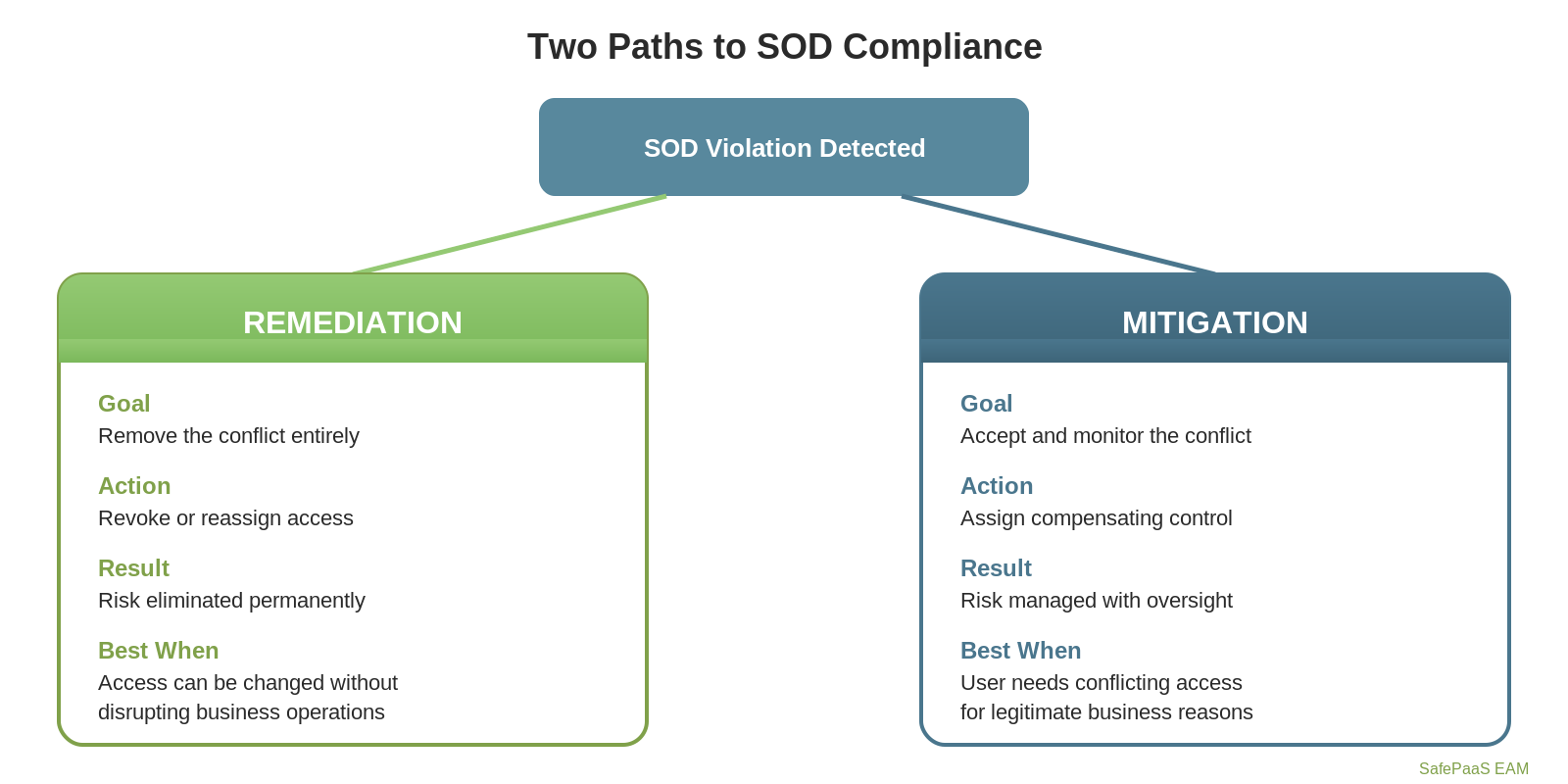
|
Aspect |
Remediation |
Mitigation |
|
Objective |
Remove the SoD conflict entirely |
Accept and monitor the SoD conflict |
|
Action |
Revoke or reassign conflicting access |
Assign a compensating control with oversight |
|
Best for |
Violations that can be resolved without business disruption |
Violations where access is operationally necessary |
|
Audit posture |
Risk eliminated |
Risk acknowledged, controlled, and monitored |
|
Time dimension |
Permanent fix (until access changes) |
Time-bound with required renewal and review |
|
Transaction visibility |
Not applicable after fix |
Ongoing monitoring of actual transactions |
Neither approach is inherently superior. A mature SoD compliance program uses both, applying remediation where possible and mitigation where necessary — with full audit trails for both.
The Mitigation Lifecycle in Segregation of Duties Compliance
A well-implemented mitigation control follows a structured lifecycle:
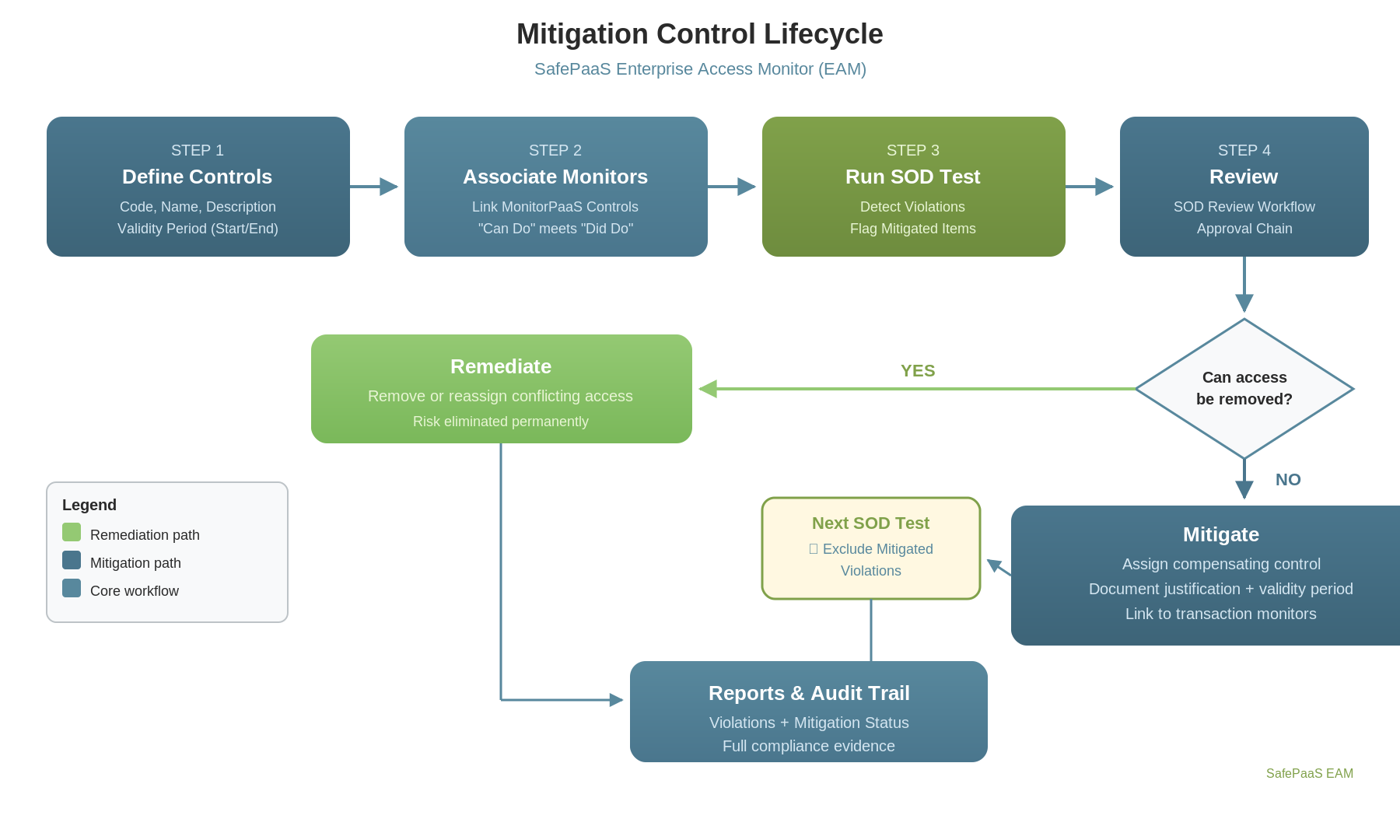
-
Define Mitigation Controls
Organizations create a catalog of mitigation controls at the company level. Each control has a code, name, description, and defined validity period. Controls can be enabled or disabled as organizational needs evolve.
-
Associate Transaction Monitors
Each mitigation control can be linked to transactional monitoring controls. This is where “can do” analysis (the SOD violation) meets “did do” analysis (actual transactions performed). If a user has conflicting access and has executed transactions using both sides of the conflict, that’s a fundamentally different risk profile than a user who simply holds the access but has never exercised it.
-
Assign to Violations
After running an SOD test, compliance teams review the results and assign mitigation controls to violations that cannot be remediated. The assignment includes a justification, supporting documentation, and date bounds that must fall within the control’s validity period.
-
Integrate with SoD Testing
During subsequent SOD test runs, the system recognizes which violations have active mitigation assignments. Organizations can choose to either flag mitigated violations in the standard report (with clear indicators showing the mitigation status) or exclude them from the primary report entirely while capturing them in a dedicated “Excluded Mitigated Violations” report.
-
Review Through SoD Surveys
During periodic SOD review cycles, reviewers see both remediation and mitigation options. They can choose the appropriate treatment for each violation, with justification required in both cases. The review survey captures the action taken, the control or plan applied, and the reviewer’s rationale.
-
Report and Audit
Violation reports include mitigation status columns — whether the violation is mitigated, which control is applied, and the associated justification. This gives auditors clear visibility into how the organization is managing accepted risk.
Why Mitigation Controls Matter for Audit Readiness
External auditors don’t just want to see that SoD violations were detected. They want to see what was done about them. An organization that detects 500 violations but only remediates 100 — with no documented treatment for the remaining 400 — faces uncomfortable audit conversations.
Mitigation controls transform those 400 unresolved violations into 400 managed risks. Each one has a documented control, a validity period, a justification, an assigned owner, and potentially a linked transaction monitor providing continuous oversight. That’s the difference between a control gap and a defensible compliance posture.
Key audit benefits include:
- Complete risk treatment coverage: Every violation is either remediated or mitigated — nothing falls through the cracks
- Time-bound accountability: Mitigation controls expire, forcing periodic reassessment rather than indefinite acceptance
- Transaction-level evidence: Linked monitors provide evidence of whether mitigated access was actually used, adding depth to the risk assessment
- Clear separation of concerns: Reports distinguish between remediated and mitigated violations, giving auditors exactly the transparency they need
The Evolution from “Can Do” to “Did Do”
Traditional SOD analysis answers one question: “Can this user perform conflicting actions?” That’s the “can do” analysis. But access alone doesn’t create loss. Risk materializes when a user actually performs conflicting transactions.
Mitigation controls bridge this gap by associating SoD violations with transaction monitoring. When a mitigation control is linked to a transactional monitor, organizations gain visibility into whether the accepted risk is theoretical or actual. A user who holds conflicting access but has never exercised both sides presents a different risk than one who routinely processes transactions on both sides of a conflict.
This “did do” visibility is what transforms mitigation from a compliance checkbox into genuine risk management.
Best Practices for Implementing Mitigation Controls
Start with a clean SoD baseline. Run your SoD analysis, remediate what you can, and then apply mitigation controls to the remainder. Don’t use mitigation as an excuse to skip remediation.
Keep mitigation controls time-bound. A mitigation control that never expires becomes a permanent risk acceptance without review. Set meaningful validity periods and enforce renewal.
Require justification. Every mitigation assignment should document why remediation isn’t feasible and what the compensating control actually monitors. This documentation is invaluable during audits.
Link to transaction monitors. Mitigation controls are most powerful when connected to real-time monitoring. The combination of “can do” detection and “did do” monitoring creates a comprehensive risk picture.
Review regularly. Include mitigation controls in your SoD review cycle. Circumstances change — a violation that couldn’t be remediated last quarter may be resolvable now.
Conclusion
Segregation of Duties compliance isn’t binary. The real world demands a spectrum of risk treatment options. Remediation handles the violations you can fix. Mitigation controls handle the ones you can’t — with structure, accountability, and continuous monitoring.
Organizations that implement both approaches create a compliance program that’s not just thorough, but realistic. And in a regulatory environment that demands increasing rigor, that combination of thoroughness and pragmatism is exactly what auditors want to see.