When Oracle ERP sits at the center of your business, ITGC and SOX work is never standing still. Oracle ERP Cloud and Oracle-native controls (such as Oracle Risk Management Cloud) may be running smoothly. However, questions increasingly focus on independent, easy-to-defend evidence that is not solely generated and maintained within the same application environment.
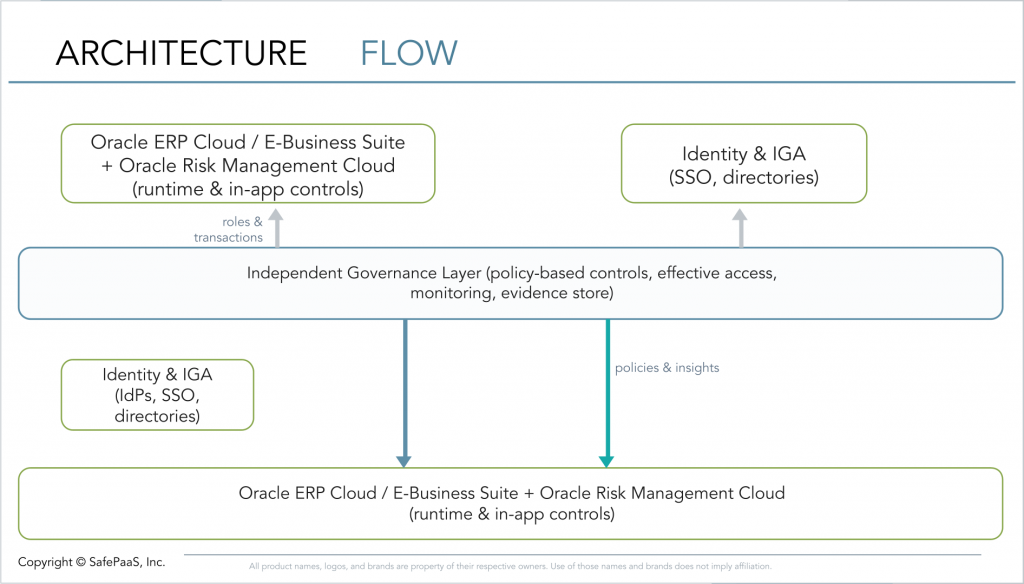
This is not a criticism of your Oracle setup or your team. It is a sign that expectations have shifted: the same system that processes transactions is now expected to “prove” its own controls, often in complex, multi‑ledger, multi‑BU environments. An independent, policy-based governance layer (operating outside the Oracle application stack, typically using extracted or replicated data for monitoring and evidence generation) is one way teams are closing that gap, without undoing years of good work in Oracle.
The questions below are designed for Oracle IT‑ERP leaders, Internal Audit, and SOX managers who want a constructive way to talk about these challenges together. Skim them and notice where you feel a bit of tension—that is usually where expectations and architecture are out of sync, not where anyone has failed.
Does your evidence story reflect how much work you’re already doing in Oracle?
Most teams already rely heavily on Oracle‑native tools for SoD and access monitoring—and rightly so. Those tools give you the operational visibility you need day‑to‑day, even if they don’t always translate neatly into the kind of independent evidence auditors now ask for.
If this sounds familiar:
- You can show detailed Oracle reports, but still end up explaining “how the system works” in every audit.
- You feel like the quality of your work is higher than what the evidence story conveys.
An independent layer isn’t about replacing Oracle RMC or similar tools; it’s about helping them “speak auditor” on your behalf.
Do reviews happen when the business changes or only when the audit calendar says so?
You know your Oracle environment doesn’t stand still — roles change, new entities come online, and integrations are added. Yet SoD and access reviews often cluster around audit timelines, simply because that’s when everyone can make time and gather spreadsheets.
Common experience:
- IT‑ERP feels pressure to “freeze” changes before audits.
- Audit and SOX worry about what might have shifted between point‑in‑time reviews.
Continuous monitoring from an independent layer, separate from Oracle’s native monitoring capabilities, helps keep pace with the business without requiring teams to run additional manual reviews.
Are cross‑system risks harder to explain than you’d like?
You’ve probably invested heavily in getting Oracle right. The trickier conversations often come when processes span Oracle and tools like Coupa, Salesforce, ServiceNow, or Kyriba, and you’re asked to explain the whole picture in one story.
Typical pattern:
- Each system on its own looks well-controlled.
- The hard part is answering “What does this mean across the end‑to‑end process?”
A governance layer that sits above Oracle and key connected applications, aggregating and analyzing access and transaction data across systems, lets you show that cross‑system view without asking every team to change their tools or workflows.
When auditors ask “Where does this evidence come from?”, do you feel like you’re on the back foot?
You may have solid Oracle reports and dashboards, but still feel the need to explain why it’s okay that evidence comes from the same system under test. That can be frustrating when you know your controls are operating well.
Many teams tell us:
- “We’re comfortable with our controls, but the independence conversation keeps coming back.”
- “It feels like we’re defending Oracle, when really we’ve just followed a standard pattern.”
An independent, policy‑based layer helps you move that discussion from “Let us explain” to “Here’s how evidence is generated and controlled outside Oracle’s runtime, using independently governed data processing and monitoring logic,” which usually lands better with auditors.
Does it feel hard to tell the story of the control operation across the whole year?
You might have good snapshots—month‑end or quarter‑end reports, evidence packs, issue logs. What’s harder is stitching that into a clear, period‑wide narrative that everyone (IT‑ERP, Audit, SOX, auditors) can see the same way.
Typical pain points:
- IT‑ERP has one view of what changed when; Audit/SOX has another.
- Pulling together a “year in review” for access and SoD takes a surprising amount of effort.
Continuous monitoring in an independent layer can help you build that shared narrative automatically, using the data you already have.
Do elevated Oracle accesses feel “controlled but hard to prove”?
Most teams manage elevated access thoughtfully: admin roles are limited, temporary overrides are approved, project access is documented. The challenge is less about what you’re doing and more about how easily you can show that it was appropriately used.
You might recognize this:
- You can show who had elevated access and why, but not always in a way that is easily correlated, reported, and evidenced for audit purposes.
- Discussions about mitigations feel more qualitative than you’d like.
An independent monitoring layer can connect those elevated accesses to actual activity and to mitigating controls, making your existing discipline more visible and defensible.
When someone asks, “Did any of this actually cause a problem?”, how easy is it to answer?
You already track potential risk—SoD conflicts, elevated access, exceptions. What’s less straightforward is answering the follow‑up: “Did any of this actually result in misuse or a control failure during the period?”
Common experience:
- IT‑ERP can show the list of conflicts; Audit/SOX can show how they were reviewed.
- It takes extra work to tie those to real transaction activity and say, confidently, “Here’s what did and did not happen.”
Independent platforms that link access, conflicts, and actual transactions can turn that into a routine query instead of a mini‑investigation.
Do you feel like you’re doing “spreadsheet heroics” to get over the line before each audit?
Behind most successful Oracle audits is a lot of behind-the-scenes effort, extracts, reconciliations, manual checks, and shared drives full of files.
This often reflects gaps between operational reporting in Oracle and the format, traceability, and aggregation that auditors expect, especially when combining access, Segregation of Duties, and transaction data into a single evidence set.
It works, but it’s fragile and heavily dependent on a few key people knowing “how it all hangs together.”
Signs this is happening:
- The same names get tagged whenever an auditor has a question about Oracle access.
- Everyone agrees the process is too manual, but changing it feels risky.
An independent, policy‑driven governance layer lets you keep the substance of what you’re doing while removing the manual stitching from the middle.
Do IT‑ERP, Internal Audit, and SOX have a shared view of “good enough”?
Most teams have informal views on maturity: “we’re okay,” “we’re a bit behind,” “we’re ahead of others.” But it’s rare for IT‑ERP, Audit, and SOX to have the same, explicit picture of where they are today and what “good” looks like for their specific Oracle footprint.
If this resonates:
- You sometimes talk past each other—IT‑ERP focusing on system design, Audit on evidence, SOX on testing.
- It’s hard to justify investments because there’s no agreed‑upon target state.
Using a simple, shared model—foundational, emerging, established, leading—can turn those feelings into a plan. An independent governance layer can become one of the enabling steps from “we’re doing the right things, but it’s hard to prove” to “we’re doing the right things, and it shows.”
A Next Step That Respects the Work You’ve Already Done
If several of these questions felt close to home, it doesn’t mean your Oracle controls are broken. It usually means your teams have done the right things within Oracle, and now expectations around independence and continuous monitoring have moved up a level.
One practical way forward is to bring these nine questions into a short working session with your Oracle IT‑ERP lead, your Internal Audit lead, and your SOX manager. Use them as a neutral framework to highlight where you’re strong, where things feel harder than they should, and where an independent, policy‑based governance layer could make your existing work easier to explain and defend.