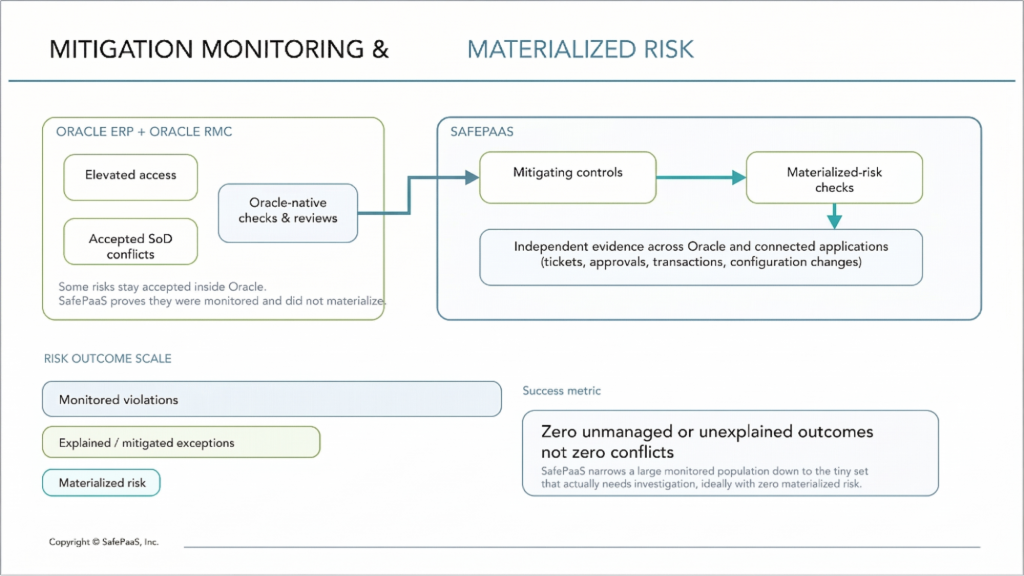
The Two Control Gaps Oracle Risk Management Cloud (RMC) Can’t Provide: Mitigation, Monitoring, and Materialized Risk Detection
Your Oracle environment will always have some elevated access. The real question is whether you can show it was controlled, monitored, and not misused over time.
Problem: Some Oracle risks can’t be removed
Some Oracle Segregation of Duties (SoD) conflicts and elevated roles are structurally necessary, not fixable. Project teams, close teams, and support admins often need powerful access combinations that keep the business running but create theoretical exposure.
Oracle Risk Management Cloud helps you define rules and run SoD and access checks inside Oracle, but it is constrained by the same role, inheritance, and data security model that created those conflicts. That means a layer of risk will always be “accepted” rather than removed, and the real test becomes whether you can show those accepted risks were actively mitigated and did not materialize into loss, misstatement, or fraud.
Gap 1: Mitigation monitoring
Most teams document mitigations; fewer can prove they actually operated for every user and every period.
When you accept an Oracle conflict or an elevated role, you typically attach a mitigating control, such as:
- A manual review or reconciliation.
- A ticketed workflow or secondary approval.
- A detective report or exception-based review.
Oracle RMC can record conflicts and run reviews, but it does not provide an independent governance layer that continuously links risky Oracle access to monitoring controls across Oracle and connected applications.
SafePaaS reconstructs effective access for Oracle and key surrounding systems outside the Oracle runtime, using roles, inheritance, and data policies so that mitigations map to real exposure rather than just role labels.
In SafePaaS, mitigating controls are first-class objects: you associate each high-risk privilege or conflict with a defined control (reconciliation, approval workflow, detective report), then automatically test whether that control executed for every relevant user and period. Accepted risks move from static exception logs and spreadsheets to a living map between elevated Oracle access and the controls that keep it under watch.
Gap 2: Materialized-risk detection
Auditors increasingly want proof of what happened, not just who could have acted. Materialized risk means being able to say, for a defined window—month-end close, project cutover, emergency access—whether specific Oracle access was actually abused.
Native Oracle and Oracle RMC reporting can show assigned access and some activity, but they are not designed to independently correlate:
- Effective access across roles and inherited privileges.
- Cross-system approvals and tickets.
- In-period transactions across Oracle and connected apps like Coupa or ServiceNow.
SafePaaS ingests Oracle access, configuration changes, and transaction data alongside non-Oracle signals (tickets, approvals, exceptions) and lets you run period-specific queries that join access, exceptions, and activity.
You can ask questions like, “For all users who had the ability to both create and pay vendors during the Q4 close, show any postings over our materiality threshold and the upstream approvals,” and get a defensible answer from one place.
For temporary or emergency access, SafePaaS can show who was elevated, what they did during the elevation window, and whether any actions fell outside the approved pattern, turning a mini-investigation into a routine query.
How SafePaaS closes the loop
Mitigation monitoring and materialized-risk detection only deliver when they work as a loop.
- Identify elevated Oracle access or SoD conflicts that cannot be removed and link each to specific mitigating controls in SafePaaS (secondary approvals, reconciliations, ticket-based workflows).
- Monitor those mitigations continuously across Oracle and key connected applications, with SafePaaS generating evidence independently of Oracle’s runtime.
- Prove during any audit period that controls operated and that underlying risky access did not result in materialized loss or control failure, using traceable, period-specific evidence generated outside the system under test.
A common scenario is a finance lead receiving temporary elevation during a project cutover to post high-risk journals. In SafePaaS, that elevation is captured, linked to a mitigating control (a post-cutover review of postings over a threshold), and monitored so that at quarter-end you can show exactly which postings occurred, how they were approved, and that none violated policy.
For cross-system processes—vendor requests in ServiceNow, approvals in Coupa, and payments in Oracle—SafePaaS correlates elevated Oracle access with upstream requests and downstream payments to demonstrate that no orphan or unauthorized transactions slipped through during the period.
Scale and independence in practice
At scale, this model changes the story you tell about elevated access.
- Teams move from thousands of theoretical SoD conflicts to a smaller population based on effective access, with SafePaaS monitoring the remainder through linked mitigations and activity checks.
- Teams shift from sampling a subset of elevated users to continuously monitoring 100% of elevated access and SoD conflicts, with SafePaaS flagging only the handful of cases where access and activity together suggest materialized risk.
- Over time, they can point to large populations of accepted conflicts or emergency elevations where monitoring controls executed and no materialized loss or fraud indicators were detected, with all evidence generated outside the system under test.
- Oracle Risk Management Cloud vs Independent Control Platforms: What’s the Difference?
- How to Evaluate Oracle ERP Security and Controls Platforms Beyond Native Tools
Next step: Audit & Compliance Playbook
If these gaps sound familiar, the next step is to turn them into an audit-ready plan that your Oracle IT-ERP leaders, Internal Audit, and SOX managers can execute together.
From Oracle-Native to Audit-Ready: A Big-4 Playbook for Internal Audit and SOX shows how to:
- Map typical Oracle IT General Controls (ITGC) and SoD finding patterns to SafePaaS capabilities for mitigation, monitoring, and materialized-risk detection.
- Keep running core controls in Oracle RMC while elevating the independence, coverage, and quality of the evidence you present to auditors.
- Move from spreadsheet-driven evidence packs to an independent, policy-driven governance layer that generates audit-ready evidence on demand.
Download
Not ready for a full playbook? See how SafePaaS turns elevated-access and SoD risk into audit-ready evidence in a short demo.